Bug in Popular WinRAR Software Could Let Attackers Hack Your Computer
A new security weakness has been disclosed in the WinRAR trialware file archiver utility for Windows that could be abused by a remote attacker to execute arbitrary code on targeted…
Before and After a Pen Test: Steps to Get Through It
An effective cybersecurity strategy can be challenging to implement correctly and often involves many layers of security. Part of a robust security strategy involves performing what is known as a…
US judge sentences duo for roles in running bulletproof hosting service
The hosting service was used to deploy malware payloads including Zeus and the Blackhole exploit kit. Read more from the Source
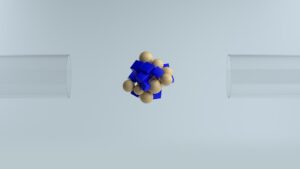
Researchers Break Intel SGX With New ‘SmashEx’ CPU Attack Technique
A newly disclosed vulnerability affecting Intel processors could be abused by an adversary to gain access to sensitive information stored within enclaves and even run arbitrary code on vulnerable systems.…